CCNA 1 Final Exam V6.0 Answers
1. Refer to the exhibit. If host A sends an IP packet to host B, what will the destination address be in the frame when it leaves host A?
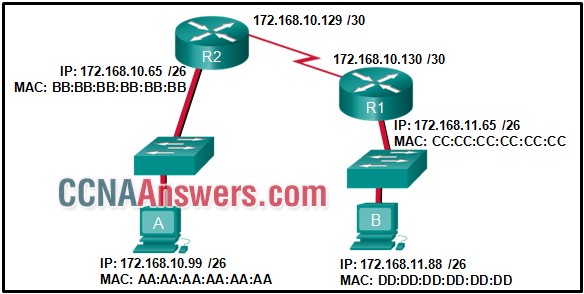
172.168.10.99
172.168.10.65
DD:DD:DD:DD:DD:DD
AA:AA:AA:AA:AA:AA
BB:BB:BB:BB:BB:BB
CC:CC:CC:CC:CC:CC
2. Which example of malicious code would be classified as a Trojan horse?
malware that was written to look like a video game
malware that requires manual user intervention to spread between systems
malware that can automatically spread from one system to another by exploiting a vulnerability in the target
malware that attaches itself to a legitimate program and spreads to other programs when launched
3. Which name is assigned to the transport layer PDU?
data
packet
frame
bits
segment
4. Which statement is true about variable-length subnet masking?
Subnets may only be subnetted one additional time.
The size of each subnet may be different, depending on requirements
Each subnet is the same size.
Bits are returned, rather than borrowed, to create additional subnets.
5. A user opens three browsers on the same PC to access www.cisco.com to search for certification course information. The Cisco web server sends a datagram as a reply to the request from one of the web browsers. Which information is used by the TCP/IP protocol stack in the PC to identify which of the three web browsers should receive the reply?
the destination port number
the source IP address
the destination IP address
the source port number
6. What is a characteristic of a fault tolerant network?
A network that protects confidential information from unauthorized access
a network that supports a mechanism for managing congestion and ensuring reliable delivery of content to all users
a network that can expand quickly to support new users and applications without impacting the performance of the service delivered to existing users
a network that recovers quickly when a failure occurs and depends on redundancy to limit the impact of a failure
7. Which two tasks are functions of the presentation layer? (Choose two.)
encryption
compression
authentication
session control
addressing
8. Which connection provides a secure CLI session with encryption to a Cisco switch?
an SSH connection
a Telnet connection
an AUX connection
a console connection
9. Which frame forwarding method receives the entire frame and performs a CRC check to detect errors before forwarding the frame?
store-and-forward switching
fragment-free switching
cut-through switching
fast-forward switching
10. What is a key characteristic of the peer-to-peer networking model?
network printing using a print server
resource sharing without a dedicated server
social networking without the Internet
wireless networking
11. What is a characteristic of the LLC sublayer?
It defines software processes that provide services to the physical layer.
It provides the logical addressing required that identifies the device.
It places information in the frame allowing multiple Layer 3 protocols to use the same network interface and media.
It provides delimitation of data according to the physical signaling requirements of the medium.
12. What are the three primary functions provided by Layer 2 data encapsulation? (Choose three.)
placement and removal of frames from the media
data link layer addressing
delimiting groups of bits into frames
conversion of bits into data signals
error correction through a collision detection method
detection of errors through CRC calculations
session control using port numbers
13. A site administrator has been told that a particular network at the site must accommodate 126 hosts. Which subnet mask would be used that contains the required number of host bits?
255.255.255.0
255.255.255.240
255.255.255.224
255.255.255.128
14. An administrator uses the Ctrl-Shift-6 key combination on a switch after issuing the ping command. What is the purpose of using these keystrokes?
To restart the ping process
to exit to a different configuration mode
to allow the user to complete the command
to interrupt the ping process
15. How many valid host addresses are available on an IPv4 subnet that is configured with a /26 mask?
64
192
62
254
190
16. Where are Cisco IOS debug output messages sent by default?
console line
memory buffers
Syslog server
vty lines
17. Which two OSI model layers have the same functionality as two layers of the TCP/IP model? (Choose two.)
physical
transport
session
data link
network
18. What are three characteristics of multicast transmission? (Choose three.)
A single packet can be sent to a group of hosts.
Routers will not forward multicast addresses in the range of 224.0.0.0 to 224.0.0.255
Multicast transmission can be used by routers to exchange routing information.
The source address of a multicast transmission is in the range of 224.0.0.0 to 224.0.0.255.
Computers use multicast transmission to request IPv4 addresses.
Multicast messages map lower layer addresses to upper layer addresses.
19. Which scenario describes a function provided by the transport layer?
A student has two web browser windows open in order to access two web sites. The transport layer ensures the correct web page is delivered to the correct browser window.
A corporate worker is accessing a web server located on a corporate network. The transport layer formats the screen so the web page appears properly no matter what device is being used to view the web site.
A student is playing a short web-based movie with sound. The movie and sound are encoded within the transport layer header.
A student is using a classroom VoIP phone to call home. The unique identifier burned into the phone is a transport layer address used to contact another network device on the same network.
20. What will a host on an Ethernet network do if it receives a frame with a destination MAC address that does not match its own MAC address?
It will remove the frame from the media.
It will discard the frame
It will strip off the data-link frame to check the destination IP address.
It will forward the frame to the next host.
21. A network administrator is troubleshooting connectivity issues on a server. Using a tester, the administrator notices that the signals generated by the server NIC are distorted and not usable. In which layer of the OSI model is the error categorized?
physical layer
network layer
data link layer
presentation layer
22. A network administrator is measuring the transfer of bits across the company backbone for a mission critical financial application. The administrator notices that the network throughput appears lower than the bandwidth expected. Which three factors could influence the differences in throughput? (Choose three.)
the sophistication of the encapsulation method applied to the data
the reliability of the gigabit Ethernet infrastructure of the backbone
the latency that is created by the number of network devices that the data is crossing
the amount of traffic that is currently crossing the network
the type of traffic that is crossing the network
the bandwidth of the WAN connection to the Internet
23. Which subnet would include the address 192.168.1.96 as a usable host address?
192.168.1.32/27
192.168.1.32/28
192.168.1.64/26
192.168.1.64/29
24. What are two functions of NVRAM? (Choose two.)
to contain the running configuration file
to retain contents when power is removed
to store the routing table
to store the ARP table
to store the startup configuration file
25. A network technician suspects that a particular network connection between two Cisco switches is having a duplex mismatch. Which command would the technician use to see the Layer 1 and Layer 2 details of a switch port?
show running-config
show ip interface brief
show interfaces
show mac-address-table
26. What are two ways that TCP uses the sequence numbers in a segment? (Choose two.)
to identify missing segments at the destination
to reassemble the segments at the remote location
to limit the number of segments that can be sent out of an interface at one time
to determine if the packet changed during transit
to specify the order in which the segments travel from source to destination
27. What are two services provided by the OSI network layer? (Choose two.)
encapsulating PDUs from the transport layer
placement of frames on the media
routing packets toward the destination
collision detection
performing error detection
28. A network team is comparing physical WAN topologies for connecting remote sites to a headquarters building. Which topology provides high availability and connects some, but not all, remote sites?
hub and spoke
partial mesh
mesh
point-to-point
29. What is a characteristic of UTP cabling?
cladding
woven copper braid or metallic foil
cancellation
immunity to electrical hazards
30. What is a benefit of using cloud computing in networking?
Home networking uses existing electrical wiring to connect devices to the network wherever there is an electrical outlet, saving the cost of installing data cables.
End users have the freedom to use personal tools to access information and communicate across a business network.
Network capabilities are extended without requiring investment in new infrastructure, personnel, or software.
Technology is integrated into every-day appliances allowing them to interconnect with other devices, making them more ‘smart’ or automated.
31. What is the function of the shell in an OS?
It interacts with the device hardware.
It provides the intrusion protection services for the device.
It provides dedicated firewall services.
It interfaces between the users and the kernel.
32. A PC obtains its IP address from a DHCP server. If the PC is taken off the network for repair, what happens to the IP address configuration?
The address lease is automatically renewed until the PC is returned.
The configuration is held by the server to be reissued when the PC is returned.
The address is returned to the pool for reuse when the lease expires.
The configuration is permanent and nothing changes.
33. A network technician is attempting to configure an interface by entering the following command: SanJose(config)# ip address 192.168.2.1 255.255.255.0. The command is rejected by the device. What is the reason for this?
The subnet mask information is incorrect.
The command syntax is wrong.
The command is being entered from the wrong mode of operation.
The interface is shutdown and must be enabled before the switch will accept the IP address.
34. When applied to a router, which command would help mitigate brute-force password attacks against the router?
login block-for 60 attempts 5 within 60
service password-encryption
banner motd $Max failed logins = 5$
exec-timeout 30
35. What purpose does NAT64 serve in IPv6?
It converts IPv6 packets into IPv4 packets.
It converts regular IPv6 addresses into 64-bit addresses that can be used on the Internet.
It converts the 48-bit MAC address into a 64-bit host address that can be used for automatic host addressing.
It enables companies to use IPv6 unique local addresses in the network.
It translates private IPv6 addresses into public IPv6 addresses.
36. What method is used to manage contention-based access on a wireless network?
CSMA/CA
CSMA/CD
token passing
priority ordering
37. What are two characteristics of fiber-optic cable? (Choose two.)
It is more expensive than UTP cabling is.
It is not affected by EMI or RFI.
It combines the technique of cancellation, shielding, and twisting to protect data.
It typically contains 4 pairs of fiber-optic wires.
Each pair of cables is wrapped in metallic foil.
38. Refer to the exhibit. Match the packets with their destination IP address to the exiting interfaces on the router. (Not all options are used.)
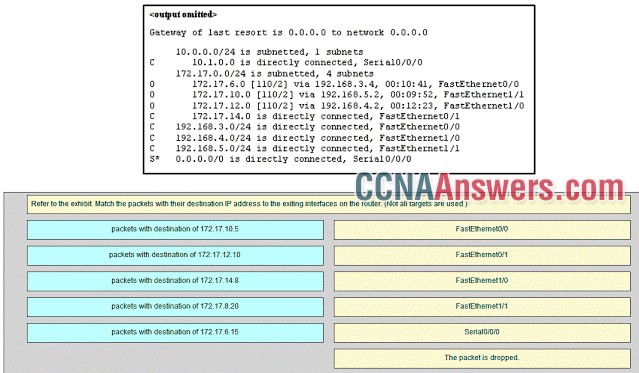
FastEthernet0/0 -> packets with destination of 172.17.6.15
FastEthernet0/1 -> packets with destination of 172.17.14.8
FastEthernet1/0 -> packets with destination of 172.17.12.10
FastEthernet1/1 -> packets with destination of 172.17.10.5
Serial0/0/0 -> packets with destination of 172.17.8.20
39. What are two benefits of using a layered network model? (Choose two.)
It speeds up packet delivery.
It prevents designers from creating their own model.
It ensures a device at one layer can function at the next higher layer.
It assists in protocol design.
It prevents technology in one layer from affecting other layers.
40. What addresses are mapped by ARP?
destination IPv4 address to the source MAC address
destination IPv4 address to the destination host name
destination MAC address to a destination IPv4 address
destination MAC address to the source IPv4 address
41. What is the most compressed representation of the IPv6 address 2001:0000:0000:abcd:0000:0000:0000:0001?
2001:0000:abcd::1
2001:0:abcd::1
2001:0:0:abcd::1
2001::abcd::1
2001::abcd:0:1
42. On which switch interface would an administrator configure an IP address so that the switch can be managed remotely?
vty 0
FastEthernet0/1
VLAN 1
console 0
43. Which domain name would be an example of a top-level domain?
cisco.com
root.cisco.com
.com
www.cisco.com
44. What is an advantage to using a protocol that is defined by an open standard?
An open standard protocol is not controlled or regulated by standards organizations.
The protocol can only be run on equipment from a specific vendor.
It encourages competition and promotes choices.
A company can monopolize the market.
45. Refer to the exhibit. What will be the result of entering this configuration the next time a network administrator connects a console cable to the router and no additional commands have been entered?
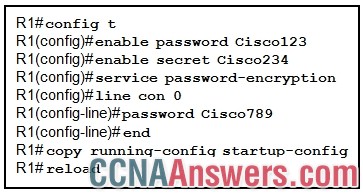
The administrator will be required to enter Cisco123.
The administrator will be required to enter Cisco789.
The administrator will be required to enter Cisco234.
The administrator will be presented with the R1> prompt
46. Three bank employees are using the corporate network. The first employee uses a web browser to view a company web page in order to read some announcements. The second employee accesses the corporate database to perform some financial transactions. The third employee participates in an important live audio conference with other corporate managers in branch offices. If QoS is implemented on this network, what will be the priorities from highest to lowest of the different data types?
Audio conference, web page, financial transactions
financial transactions, web page, audio conference
financial transactions, audio conference, web page
audio conference, financial transactions, web page
47. Which range of link-local addresses can be assigned to an IPv6-enabled interface?
FEC0::/10
FE80::/10
FDEE::/7
FF00::/8
48. Refer to the exhibit. A network administrator is configuring access control to switch SW1. If the administrator uses a console connection to connect to the switch, which password is needed to access user EXEC mode?
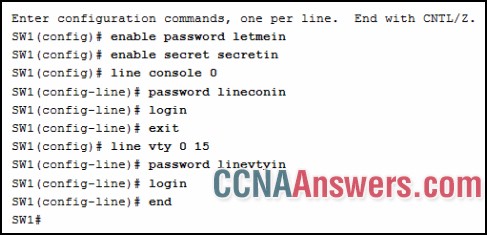
secretin
letmein
lineconin
linevtyin
49. What are the three ranges of IP addresses that are reserved for internal private use? (Choose three.)
192.168.0.0/16
192.31.7.0/24
64.100.0.0/14
127.16.0.0/12
10.0.0.0/8
172.16.0.0/12
50. Match the description with the associated IOS mode. (Not all options are used.)
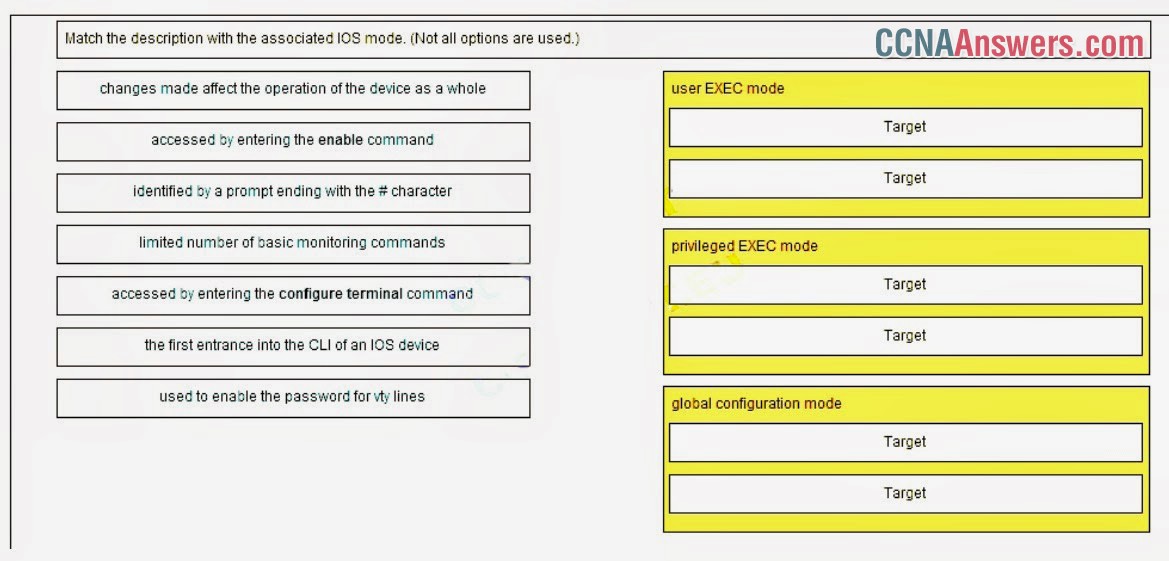
user EXEC mode
limited number of basic monitoring commands
the first entrance intro the CLI of an IOS device
privileged EXEC mode
accessed by entering the enable command
identified by a prompt ending with the # character
global configuration mode
changes made affect the operation of the device as a whole
accessed by entering the configure terminal command
51. A wireless host needs to request an IP address. What protocol would be used to process the request?
HTTP
ICMP
DHCP
SNMP
FTP
52. What is the dotted decimal representation of the IPv4 address 11001011.00000000.01110001.11010011?
198.51.100.201
203.0.113.211
209.165.201.223
192.0.2.199
53. A technician can ping the IP address of the web server of a remote company but cannot successfully ping the URL address of the same web server. Which software utility can the technician use to diagnose the problem?
ipconfig
nslookup
netstat
tracert
54. What protocol is responsible for controlling the size of segments and the rate at which segments are exchanged between a web client and a web server?
Ethernet
IP
HTTP
TCP

Leave a Reply