CCNA 4 Chapter 4 V4.0 Answers
1. Which two statements are true regarding network security? (Choose two.)
Securing a network against internal threats is a lower priority because company employees represent a low security risk.
Both experienced hackers who are capable of writing their own exploit code and inexperienced individuals who download exploits from the Internet pose a serious threat to network security.
Assuming a company locates its web server outside the firewall and has adequate backups of the web server, no further security measures are needed to protect the web server because no harm can come from it being hacked.
Established network operating systems like UNIX and network protocols like TCP/IP can be used with their default settings because they have no inherent security weaknesses.
Protecting network devices from physical damage caused by water or electricity is a necessary part of the security policy.
2. Which two statements are true about network attacks? (Choose two.)
Strong network passwords mitigate most DoS attacks.
Worms require human interaction to spread, viruses do not.
Reconnaissance attacks are always electronic in nature, such as ping sweeps or port scans.
A brute-force attack searches to try every possible password from a combination of characters.
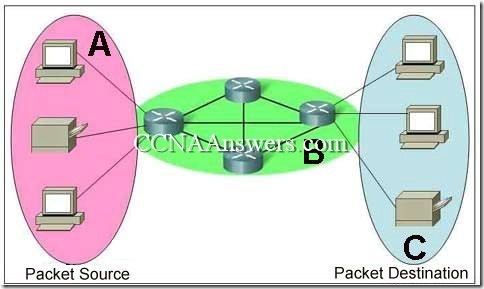
Devices in the DMZ should not be fully trusted by internal devices, and communication between the DMZ and internal devices should be authenticated to prevent attacks such as port redirection.