CCNA Discovery 3 Chapter 2 V4.0 Answers
DRSEnt Chapter 2 – CCNA Discovery: Introducing Routing and Switching in the Enterprise (Version 4.0)
1. Which two router parameters can be set from interface configuration mode? (Choose two.)
IP address
Telnet password
hostname
console password
subnet mask
enable secret password
2. An investment company has multiple servers that hold mission critical data. They are worried that if something happens to these servers, they will lose this valuable information. Which type of plan is needed for this company to help minimize loss in the event of a server crash?
business security
business continuity
network maintenance
service level agreement
3. Which three items would be found in a NOC? (Choose three.)
raised floors
all wireless access points
network monitoring station
departmental printers
customer workstations
data storage devices
4. What two features are true of an IDF? (Choose two.)
referred to as a wiring closet
located within the NOC
contains access layer devices for user connectivity
contains firewalls and content filtering devices
alternately called an MDF
5. It is crucial that network administrators be able to examine and configure network devices from their homes. Which two approaches allow this connectivity without increasing vulnerability to external attacks? (Choose two.)
Configure a special link at the POP to allow external entry from the home computer.
Set up VPN access between the home computer and the network.
Install a cable modem in the home to link to the network.
Configure ACLs on the edge routers that allow only authorized users to access management ports on network devices.
Configure a server in the DMZ with a special username and password to allow external access.
6. Which type of network map shows the location of hosts, network devices, and media?
physical topology
logical topology
control plane
business continuity
7. When searching for information about authentication methods and usernames of company personnel, where can a network administrator look?
Business Continuity Plan
Business Security Plan
Network Maintenance Plan
Service Level Agreement
8. Which two pieces of information are documented in a logical topology map? (Choose two.)
physical cabling
service level agreements
IP addressing
IDF location
group usage information
facility floor plans
9. Which two situations require a network administrator to use out-of-band management to change a router configuration? (Choose two.)
Network links to the router are down.
No Telnet password has been configured on the router.
The administrator can only connect to the router using SSH.
The network interfaces of the router are not configured with IP addresses.
Company security policy requires that only HTTPS be used to connect to routers.
10. A Cisco router needs to be configured from a remote location by the use of out-of-band management. Which method should be used?
Use Telnet or SSH and connect to an IP address of a FastEthernet port.
Use HTTP to connect to an IP address on a FastEthernet port.
Use dial up and a modem to connect to the auxiliary port.
Use a terminal emulation program and connect to the console port.
11. A network administrator needs to configure Telnet access to a router. Which group of commands enable Telnet access to the router?
Router(config)# enable password class
Router(config)# line con 0
Router(config-line)# login
Router(config-line)# password cisco
Router(config)# ip host 192.168.1.1 NewYork
Router(config)# enable password cisco
Router(config)# line aux 0
Router(config-line)# login
Router(config-line)# password cisco
Router(config)# enable password class
Router(config)# line vty 0 4
Router(config-line)# password cisco
Router(config-line)# login
12. What device is responsible for moving packets to destination networks outside the local network?
router
switch
IPS device
IDS device
13. Which two items protect a corporate network against malicious attacks at the enterprise edge ? (Choose two.)
point of demarcation
IP security (IPSec)
Data Service Unit (DSU)
intrusion prevention system (IPS)
intrusion detection system (IDS)
14. Which two types of information should be included in a business continuity plan? (Choose two.)
maintenance time periods
intrusion monitoring records
offsite data storage procedures
alternate IT processing locations
problem resolution escalation steps
15. A network administrator must define specific business processes to implement if a catastrophic disaster prevents a company from performing daily business routines. Which portion of the network documentation is the administrator defining?
business security plan
business continuity plan
network solvency plan
service level agreement
network maintenance plan
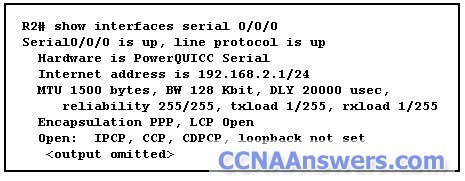
16. A network administrator has just inserted a new WIC2T controller into the first available slot of an 1841 router. The administrator needs to configure the first serial interface of this new controller. Which interface should be used?
s0/0/0
s0/0/1
s1/1/0
s1/0/1
s0/1/1
17. What information can an administrator learn using the show version command?
Cisco IOS filename
configured routing protocol
status of each interface
IP addresses of all interfaces
18. A DoS attack crippled the daily operations of a large company for 8 hours. Which two options could be implemented by the network administrator to possibly prevent such an attack in the future? (Choose two.)
install security devices with IDS and IPS at the enterprise edge
reset all user passwords every 30 days
filter packets based on IP address, traffic pattern, and protocol
deny external workers VPN access to internal resources
ensure critical devices are physically secure and placed behind the demarc
19. What type of connection point is a point of presence (POP)?
between a client and a host
between two local networks
between a computer and a switch
between an ISP and an Enterprise network
20. A network manager wants to have processes in place to ensure that network upgrades do not affect business operations. What will the network manager create for this purpose?
business security plan
business continuity plan
service level agreement
network maintenance plan
21. What is the maximum recommended cable length for Fast Ethernet over UTP?
50 meters
75 meters
100 meters
150 meters
22. Which two statements are true about a network operations center (NOC)? (Choose two.)
Most NOCs only have tower servers or desktop servers that provide high-speed storage capabilities for thousands of clients.
A NOC is typically used only to monitor and maintain the most critical network components.
Because access is secured by firewalls, backup systems are not required in a NOC .
Routers, high-speed switches, and servers are located within a NOC.
High-speed and high-capacity data storage are important aspects of a NOC.
23. What is the demarcation?
physical point where the ISP responsibility ends and the customer responsibility begins
physical location where all server farm connections meet before being distributed into the Core
point of entry for outside attacks and is often vulnerable
point of entry for all Access Layer connections from the Distribution Layer devices


Leave a Reply