CCNA 2 Module 10 V3.1 Answers
1. Which of the following describe how TCP adds reliability to communication? (Choose three.)
Hosts using TCP set up virtual circuits at the beginning of the transmission using the three-way handshake.
Hosts using TCP set the error-checking frequency at the beginning of the transmission and maintain this frequency for the duration of the data transfer.
When a sending host does not receive an acknowledgment within a timed interval it retransmits data.
The receiving host acknowledges that it has received the expected number of segments and requests additional data.
The receiving host acknowledges any incorrectly received data and requests retransmission of damaged or missing bytes.
The sending host transmits each segment twice to ensure that data is not lost.
2. A computer programmer is developing software that requires a reliable stream of data. Which protocol can be used in the software design to eliminate the need for building error detection and recovery into the application program?
TCP
IP
ICMP
UDP
HTTP
3. Why is TCP considered a connection-oriented protocol?
It establishes a virtual connection between hosts using a two-way handshake.
It uses IP to guarantee delivery of packets between hosts.
It requires hosts to go through a synchronization process prior to data transmission.
It creates a connection that depends on application layer protocols for error detection.
4. At which point in the transmission process are segments numbered?
when received
when reassembling
before transmission
while negotiating window size
5. What is dynamically assigned by the source host when forwarding data?
destination IP address
destination port number
default gateway address
source IP address
source port number
6. How are originating source port numbers assigned during the data encapsulation process?
assigned manually by the user when starting the application
assigned dynamically by the source host
assigned by the routing protocol during the lookup process
assigned by the destination host during session negotiation
7. Which of the following would an administrator do to defend against a denial of service SYN flooding attack? (Choose two.)
Hide the source of incoming IP addresses.
Decrease the connection timeout period.
Synchronize all host communication.
Increase the connection queue size.
Flood the network with false SYN requests.
8. When a host receives a data segment, what allows the host to determine which application should receive the segment?
IP source address
IP destination address
PAR
sliding window
port number
SYN packet
9. What is used by UDP to determine if the data or header has been transferred without corruption?
lower layer protocols
checksum
PAR
sliding window
acknowledgment and retransmission
IP
10. What is the purpose of using port numbers in the transport layer?
to identify the segment as being either TCP or UDP
to provide reliability during data transport
to identify the interface port number used by the router when forwarding data
to track multiple conversations that occur between hosts
11. In the TCP header, which of the following determines the amount of data that can be sent before receiving an acknowledgment?
segment number
priority number
window size
value in the length field
value in the port field
acknowledgment number
12. What does TCP use to ensure reliable delivery of data segments?
upper layer protocols
lower layer protocols
sequence numbers
port numbers
13. Which of the following protocols uses UDP for transport layer services?
SMTP
HTTP
DNS
FTP
14.
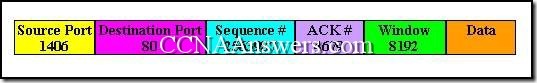
What type of segment and data is shown in the graphic?
a UDP segment carrying e-mail traffic
a TCP segment carrying FTP traffic
an IP segment carrying FTP traffic
a UDP segment carrying web traffic
a TCP segment carrying web traffic
an IP segment carrying e-mail traffic
15. What is the purpose of Positive Acknowledgment and Retransmission (PAR)?
PAR allows the presentation layer to request that data be resent in a format the destination host can process.
PAR provides a mechanism for the receiving device to request that all segments be retransmitted if one segment is corrupt.
PAR helps ensure that a number of data segments sent by one host are received by another host before additional data segments are sent.
PAR is used to renegotiate the window size during the synchronization process.
16. Which of the following are functions of the TCP protocol? (Choose three.)
translation of data
synchronization
path determination
flow control
data representation
reliability
17. What is used by both TCP and UDP when creating a segment?
IP address
MAC address
IPX address
socket or port number
acknowledgment number
sequence number
18. Which authority has control over the assignment of port numbers for applications?
IEEE
IANA
InterNIC
Software Developers Association
19. Which of the following describe types of port numbers that can be represented in the headers of TCP and UDP segments? (Choose three.)
connectionless
well-known
operational
dynamic
registered
static
20. What is the purpose of the three-way handshake that occurs between hosts using TCP as the transport layer protocol?
to increase the number of packets that can be sent before an acknowledgment is required
to allow a host to forward data to a router
to establish a round trip connection between sender and receiver before data is transferred
to provide a mechanism for data encryption and compression
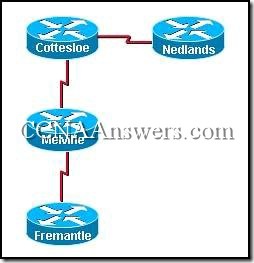
21. During the encapsulation process, in which order are the IP address, MAC address, and port number assigned when the router is establishing communication with the TFTP server?
IP address, MAC address, port number
MAC address, IP address, port number
port number, IP address, MAC address
port number, MAC address, IP address
22. Which of the following describes a type of denial of service attack designed to exploit the normal function of the TCP three-way handshake?
A host sends a packet with a spoofed source IP address.
A host sends a packet with an incorrect destination IP address.
A source sends a packet containing a garbled header.
A host sends an oversized packet that fills the memory buffers of the destination host.
A host sends a packet that contains a virus.
A host sends a packet that contains a worm.
23. Which transport layer unit of information places the port number in the header?
data
segment
packet
frame
bit


Leave a Reply