CCNA 1 Chapter 10 V6.0 Answers
1. When retrieving email messages, which protocol allows for easy, centralized storage and backup of emails that would be desirable for a small- to medium-sized business?
IMAP
POP
HTTPS
SMTP
2. Which application layer protocol uses message types such as GET, PUT, and POST?
DHCP
DNS
POP3
SMTP
HTTP
3. Two students are working on a network design project. One student is doing the drawing, while the other student is writing the proposal. The drawing is finished and the student wants to share the folder that contains the drawing so that the other student can access the file and copy it to a USB drive. Which networking model is being used?
client-based
master-slave
peer-to-peer
point-to-point
4. Fill in the blank.
The HTTP message type used by the client to request data from the web server is the _GET_ message.
5. What part of the URL, http://www.cisco.com/index.html, represents the top-level DNS domain?
www
.com
index
http
6. Which two definitions accurately describe the associated application layer protocol? (Choose two.)
HTTP – enables devices on a network to obtain IP addresses
Telnet – provides remote access to servers and networking devices
DNS – resolves Internet names to IP addresses
SMTP – transfers web pages from web servers to clients
FTP – transfers email messages and attachments
7. Match the function to the name of the application. (Not all options are used.)
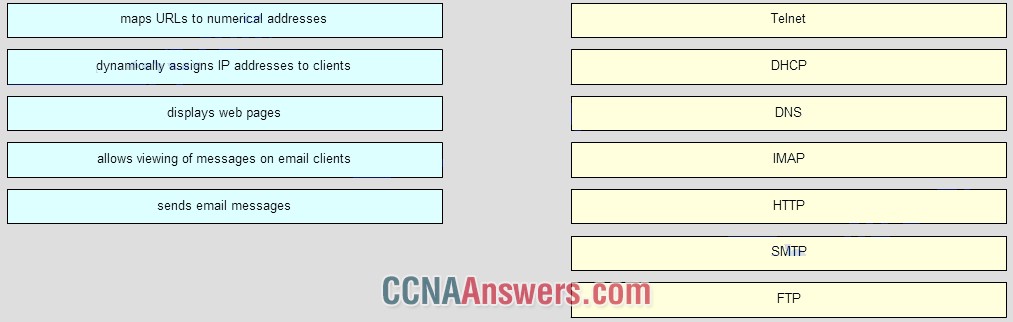
Place the options in the following order:
DHCP -> dynamically assigns IP address to clients
DNS -> maps URLs to numerical addresses
IMAP -> allows viewing of messages on email clients
HTTP -> displays web pages
SMTP -> sends email messages
8. The application layer of the TCP/IP model performs the functions of what three layers of the OSI model? (Choose three.)
session
presentation
physical
data link
transport
network
application
9. What do the client/server and peer-to-peer network models have in common?
Both models have dedicated servers.
Both models require the use of TCP/IP-based protocols.
Both models support devices in server and client roles.
Both models are used only in the wired network environment.
10. Which layer in the TCP/IP model is used for formatting, compressing, and encrypting data?
internetwork
session
application
network access
presentation
11. What is true about the Server Message Block protocol?
Different SMB message types have a different format.
Clients establish a long term connection to servers.
SMB messages cannot authenticate a session.
SMB uses the FTP protocol for communication.
12. Fill in the blank.
Refer to the exhibit. What command was used to resolve a given host name by querying the name servers?
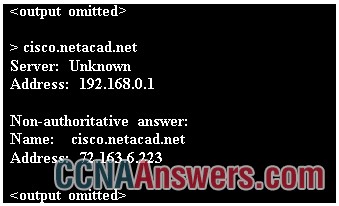
NSLOOKUP
13. What is an advantage for small organizations of adopting IMAP instead of POP?
When the user connects to a POP server, copies of the messages are kept in the mail server for a short time, but IMAP keeps them for a long time.
POP only allows the client to store messages in a centralized way, while IMAP allows distributed storage.
Messages are kept in the mail servers until they are manually deleted from the email client.
IMAP sends and retrieves email, but POP only retrieves email.
14. Open the PT Activity. Perform the tasks in the activity instructions and then answer the question.
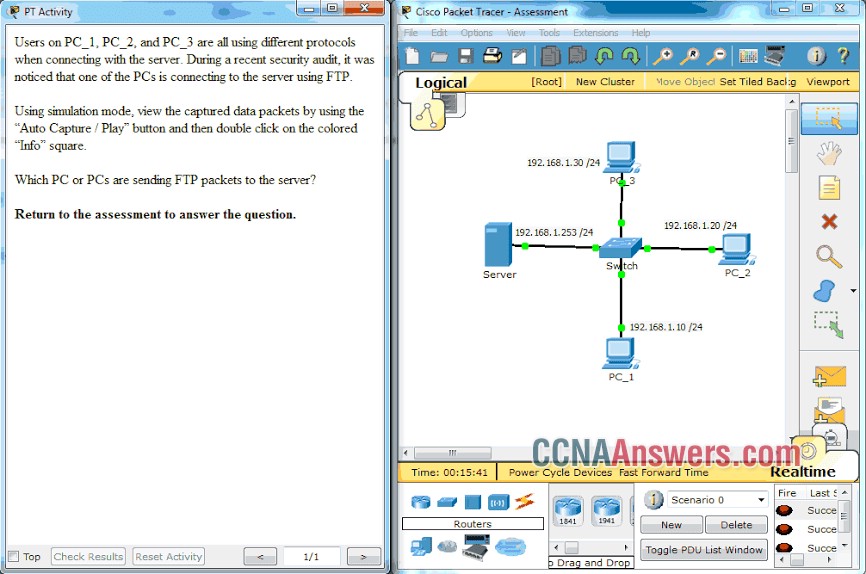
PC_3
PC_2
PC_1 and PC_3
PC_1
15. Which phrase describes an FTP daemon?
a program that is running on an FTP server
an application that is used to request data from an FTP server
a diagnostic FTP program
a program that is running on an FTP client
16. Which two tasks can be performed by a local DNS server? (Choose two.)
providing IP addresses to local hosts
allowing data transfer between two network devices
mapping name-to-IP addresses for internal hosts
forwarding name resolution requests between servers
retrieving email messages
17. Which three statements describe a DHCP Discover message? (Choose three.)
The source MAC address is 48 ones (FF-FF-FF-FF-FF-FF).
All hosts receive the message, but only a DHCP server replies.
The message comes from a client seeking an IP address.
The message comes from a server offering an IP address.
The destination IP address is 255.255.255.255.
Only the DHCP server receives the message.
18. Fill in the blank.
What is the acronym for the protocol that is used when securely communicating with a web server?
HTTPS
19. Which statement is true about FTP?
The client can choose if FTP is going to establish one or two connections with the server.
The client can download data from or upload data to the server.
FTP is a peer-to-peer application.
FTP does not provide reliability during data transmission.
20. Match a statement to the related network model. (Not all options are used.)
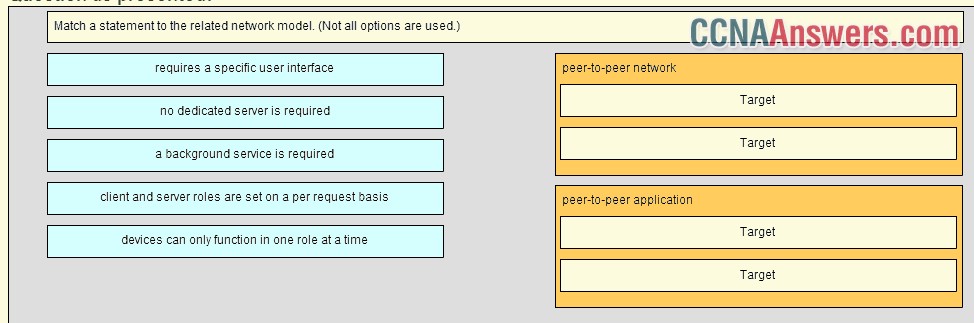
peer-to-peer network
[+] no dedicated server is required
[+] client and server roles are set on a per request basis
peer-to-peer aplication
[#] requires a specific user interface
[#] a background service is required
21. A manufacturing company subscribes to certain hosted services from its ISP. The services that are required include hosted world wide web, file transfer, and e-mail. Which protocols represent these three key applications? (Choose three.)
SNMP
SMTP
DHCP
FTP
HTTP
DNS
22. Which application layer protocol is used to provide file-sharing and print services to Microsoft applications?
SMTP
SMB
HTTP
DHCP
23. What is an example of network communication that uses the client-server model?
A user uses eMule to download a file that is shared by a friend after the file location is determined.
A workstation initiates an ARP to find the MAC address of a receiving host.
A workstation initiates a DNS request when the user types www.cisco.com in the address bar of a web browser.
A user prints a document by using a printer that is attached to a workstation of a coworker.
24. What are two characteristics of the application layer of the TCP/IP model? (Choose two.)
the establishing of window size
responsibility for physical addressing
the creation and maintenance of dialogue between source and destination applications
responsibility for logical addressing
closest to the end user

Leave a Reply