CCNA 4 Final Exam
1. Which functions are provided by LCP and NCP as part of the PPP layered architecture?
LCP sets up the PPP connection and its parameters. NCP terminates the PPP connection.
LCP sets up the PPP connection and its parameters. NCP handles higher layer protocol configurations.
LCP includes the link-establishment phase. NCP includes link-maintenance and link-termination phases.
LCP negotiates options for multiple network layer protocols. NCP agrees automatically on encapsulation formats.
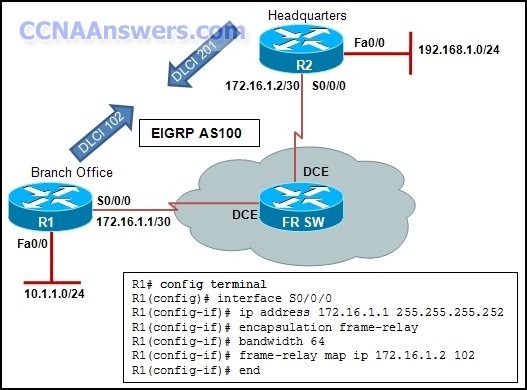
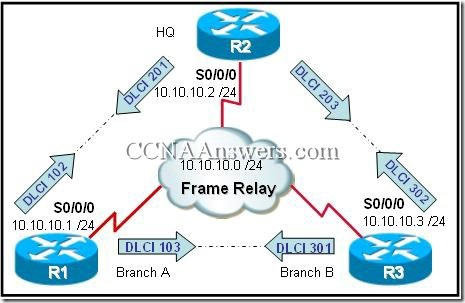
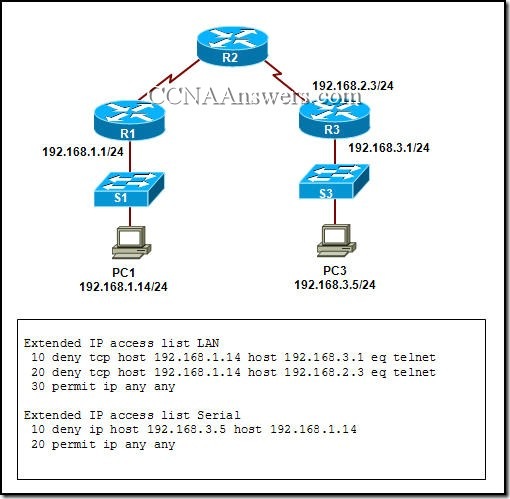
2.
Refer to the exhibit. EIGRP has been configured on routers R1 and R2. Connectivity across the Frame Relay switch between routers R1 and R2 is successfully verified using the ping command. However, no EIGRP routes are appearing in the routing table. What could be a cause for this failure?
The Frame Relay switch has failed.
The frame-relay map statement is incorrect.
The S0/0/0 interface of router R1 is administratively down.
The S0/0/0 interface of router R2 has an incorrect IP address.