CCNA Discovery 2 Final Exam V4.1 Answers
DsmbISP Final Exam - CCNA Discovery: Working at a Small-to-Medium Business or ISP (Version 4.1)
1. Which statement is true about FTP implementations?
The protocol interpreter (PI) function engages once the data transfer process (DTP) function is complete.
The DTP function is responsible for the login sequence.
FTP requires two connections, one for control and one for data.
Both the PI and the DTP close automatically when the transfer is complete.
2. A user is able to ping an FTP server across a WAN but is unable to download files from the server. What should be checked to resolve this problem?
the NIC drivers
the IP configuration
the LED status of the NIC
firewall settings
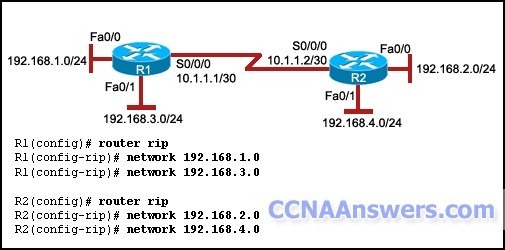
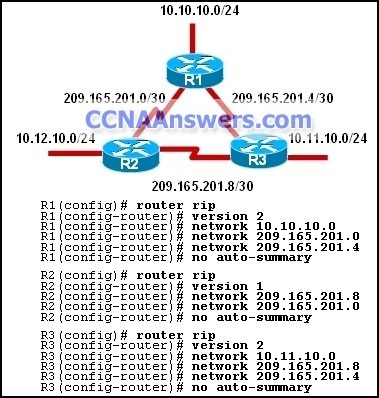
3.
Refer to the exhibit. R1 and R2 are configured with the commands that are displayed. All interfaces are properly configured, but neither router is receiving routing updates. What two things can be done to solve the problem? (Choose two.)
Configure the routing protocol on R1 for network 10.0.0.0.
Configure the routing protocol on R2 for network 10.0.0.0.
Configure the routing protocol on R1 for network 192.168.4.0.
Configure the routing protocol on R1 for network 192.168.2.0.
Configure the routing protocol on R2 for network 192.168.1.0.
Configure the routing protocol on R2 for network 192.168.3.0.
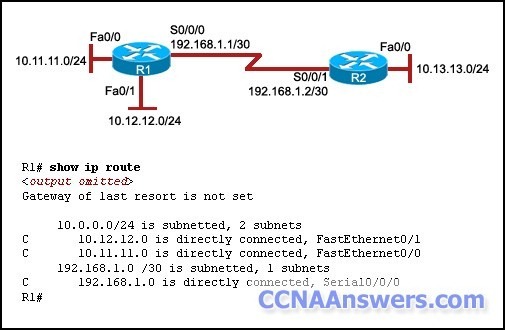
4.
Refer to the exhibit. The network administrator has added a route by using the ip route 10.13.13.0 255.255.255.0 192.168.1.1 command on R1. Hosts on the 10.12.12.0 network cannot communicate with hosts on the 10.13.13.0 network. What is the reason for this?
The gateway of last resort is not set.
The destination prefix mask is incorrectly configured.
The routing protocol has not been configured on R1.
The static route has not been configured correctly.
5. Which two statements are true about resolvers in the DNS hierarchy? (Choose two.)
The resolvers attempt to resolve client queries by using the records that the resolvers maintain in their zone database files.
The DNS server queries the resolvers to translate the domain name to an IP address.
There can be only one resolver in a DNS zone.
Resolvers may be configured on DNS clients.
The DNS server uses the resolver to forward the name resolution request to another DNS server.
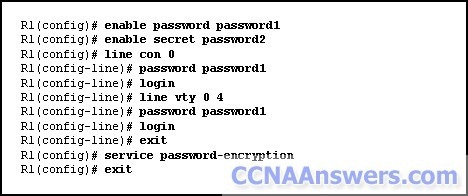
6.
Refer to the exhibit. Router R1 has been configured with the commands that are displayed. Which fact can be determined from the configuration?
All passwords are encrypted.
The privileged EXEC mode password is “password1.”
The router can support four Telnet sessions simultaneously.
The router can be accessed from the console without using any password.
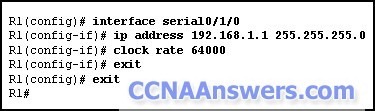
7.
Refer to the exhibit. A new router has been configured for the first time with the commands that are displayed. Which two facts can be determined about the interface of this router? (Choose two.)
It will act as a DCE device.
It is administratively down.
It will operate at a speed of 6.4 Mb/s.
It is the first interface on slot 0 of controller 1.
Because MOTD is not configured, the interface will not work.
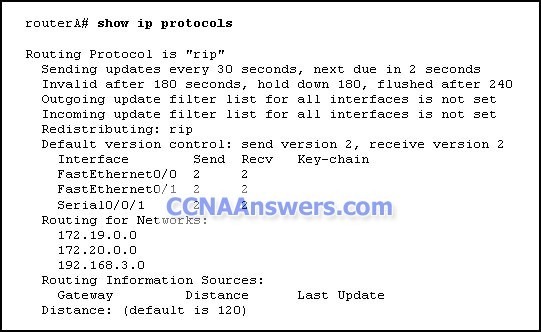
8. What are two reasons for issuing the show ip protocols command on a router? (Choose two.)
It displays the routing protocol in use.
It displays the routed protocol in use.
It displays the routing activity in real time.
It displays the static routes that are contained in the routing table.
It displays the networks that are being advertised by the router.
9. Which statement correctly describes an SLA?
It lists the terms of the agreement between the user and the manufacturer of the system.
It outlines the management, monitoring, and maintenance of a network.
It specifies the software and hardware configurations of a system.
It describes the operation of a system.
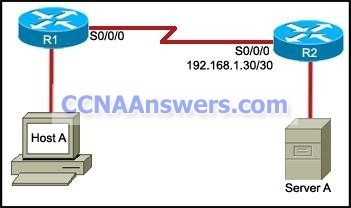
10.
Refer to the exhibit. The S0/0/0 interface of R2 is configured correctly with the default encapsulation. Which configuration should be implemented at the S0/0/0 interface of R1 to complete the connection between the two routers?
R1(config-if)# ip address 192.168.1.31 255.255.255.252
R1(config-if)# no shutdown
R1(config-if)# ip address 192.168.1.33 255.255.255.252
R1(config-if)# encapsulation PPP
R1(config-if)# no shutdown
R1(config-if)# ip address 192.168.1.28 255.255.255.252
R1(config-if)# encapsulation PPP
R1(config-if)# no shutdown
R1(config-if)# ip address 192.168.1.29 255.255.255.252
R1(config-if)# no shutdown
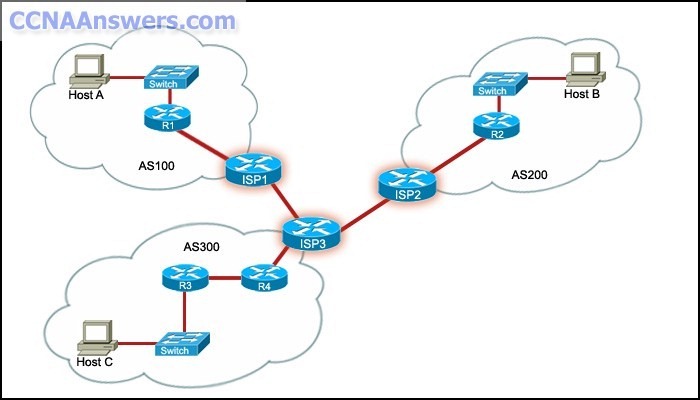
11.
Refer to the exhibit. What method is most commonly employed by large ISPs, such as ISP1, ISP2, and ISP3, to exchange and maintain routing information?
static routes
IGP protocols
EGP protocols
directly connected routes
12. Which cable should be used to connect a PC to the console port of a Cisco router?
serial
crossover
rollover
straight-through
13. What is the effect of issuing the hostname RouterA command on a router?
A description will be configured on the router interfaces identifying them as belonging to RouterA.
The router will attempt to establish a connection to the host with the name RouterA.
The router will map an IP address to the domain name RouterA.
The router prompt will change from Router(config)# to RouterA(config)#
14. Which routing protocol excludes the subnet information from routing updates?
EIGRP
OSPF
RIPv1
BGP
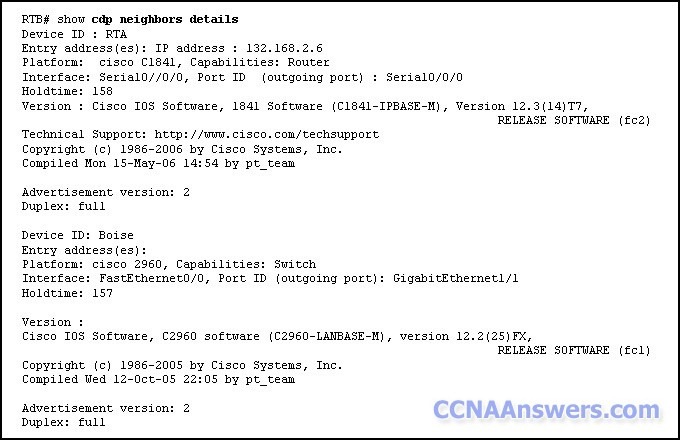
15.
Refer to the exhibit. What two conclusions can be drawn about the exhibited command output? (Choose two.)
Router RTB is directly connected to a router and a switch.
Router RTB is able to ping its directly connected neighbors.
The network administrator needs to log in to the neighboring devices to gather this information.
Router RTB has Layer 2 connectivity with two neighboring devices.
Router RTB is connected to two Cisco devices by FastEthernet links.
16. Which statement correctly describes MIB?
It is software that is installed on a device which in turn is managed by SNMP.
It is installed on a system that is used to monitor networking devices.
It is a database that a device keeps about itself concerning network performance parameters.
It is a communication protocol that is used between the management station and the management agent.
17. A customer reports connectivity problems to an ISP technician. Upon questioning the customer, the technician discovers that all network applications are functioning except for FTP. What should the technician suspect is the problem?
misconfigured firewall
bad port on switch or hub
misconfigured IP addressing on the customer's workstation
wrong DNS server configured on the customer's workstation
wrong default gateway configured on the customer's workstation
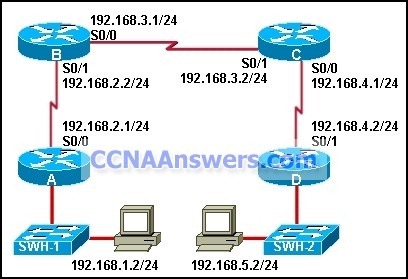
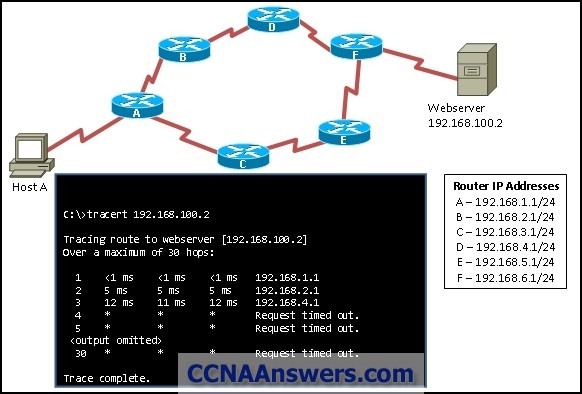
18.
The show ip route command was executed on one of the routers shown in the graphic and the following output was displayed:
C 192.168.4.0/24 is directly connected, Serial0/0
R 192.168.5.0/24 [120/1] via 192.168.4.2, 00:00:19, Serial0/0
R 192.168.1.0/24 [120/2] via 192.168.3.1, 00:00:20, Serial0/1
R 192.168.2.0/24 [120/2] via 192.168.3.1, 00:00:20, Serial0/1
C 192.168.3.0/24 is directly connected, Serial0/1
From which router was this command executed?
A
B
C
D
19. While troubleshooting a connectivity issue between two directly connected routers, the network administrator checks the encapsulation settings on the serial interfaces of both routers. Which layer of the OSI model is the administrator troubleshooting?
application layer
network layer
data link layer
physical layer
20. Which statement correctly describes the difference between HTTP and HTTPS?
The maximum number of simultaneous connections that a server can support for HTTPS is more than for HTTP.
HTTPS and HTTP use different client request-server response processes.
HTTPS authenticates and encrypts the data being transferred between the client and the web server.
HTTPS specifies the rules for passing data between the physical layer and the data link layer.
21. Which two subnet masks can be used when subnetting a Class A IP address? (Choose two.)
255.0.0.0
240.0.0.0
224.0.0.0
255.255.0.0
255.255.255.0
22. A hacker attempts to reach confidential information that is stored on a server inside the corporate network. A network security solution inspects the entire packet, determines that it is a threat, and blocks the packet from entering the inside network. Which security measure protected the network?
an IDS
an IPS
a host-based firewall
Anti-X software
23. Which statement describes a feature of TCP?
It provides low overhead data delivery.
It acknowledges the receipt of packets.
It does not provide error checking.
It is a connectionless protocol.
24. Which routing protocol depends on the DUAL algorithm to calculate the shortest path to a destination?
OSPF
EIGRP
RIP
BGP
25. What is a characteristic of Syslog?
It requires users to prove their identity with the use of a username and password before users can access network resources.
It listens to network traffic and sends an alert to a management station to track which applications are used and the length of time for which they are used.
It enables devices to send information to a daemon that runs on a management station.
It provides users the rights to access specific resources and perform specific tasks.
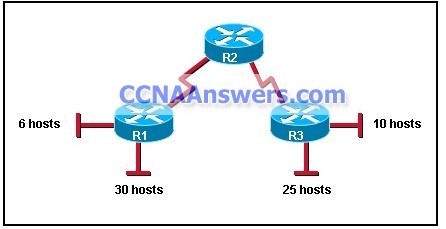
26.
Refer to the exhibit. Which subnet mask would accommodate the number of hosts indicated for all subnets if the major network address was 192.168.25.0/24?
255.255.0.0
255.255.224.0
255.255.255.0
255.255.255.224
255.255.255.240
255.255.255.248
27.
Refer to the exhibit. Devices need to connect to the file server from remote networks. What method should be used to provide the file server with an IP address to allow these connections?
static NAT
static PAT
dynamic NAT
dynamic PAT
28. Which two statements are true about the c:\> ping command? (Choose two.)
It tests the accessibility of an IP address.
It sends a TCP packet to the destination IP address.
It sends an ICMP echo request packet to the destination address.
It traces the route of a data packet from the source to the destination.
It determines where a packet was lost or delayed during transmission.
29. Which type of address is 192.168.17.111/28?
host address
network address
broadcast address
multicast address
30. Which type of cable may be used for backbone cabling between data centers that are located on different floors and that are separated by a distance of 1640 feet (500 meters)?
STP
UTP
coaxial
fiber-optic
31. Which WAN connection provides a dedicated circuit with fixed bandwidth available at all times?
point-to-point
circuit-switched
packet-switched
cable
32. When does a router enter the setup mode?
when the Cisco IOS is missing in flash
when the configuration is missing in NVRAM
when the setup command is run from the user mode
when the boot system command is missing in the configuration
33. What is a feature of PAT?
It maps IP addresses to URLs.
It displays private IP addresses to public networks.
It sends acknowledgments of received packets.
It allows multiple hosts on a single LAN to share globally unique IP addresses.
34. How many host addresses can be assigned in each subnetwork when using network address 172.16.0.0 with subnet mask 255.255.252.0?
256
510
512
1022
024
35. What are three features of the TCP protocol? (Choose three.)
It provides retransmission of data packets if they are lost during transmission.
It is a connectionless protocol.
It uses a three-way handshake between the sending and receiving systems to establish each conversation.
It specifies how messages are reassembled at the destination host.
It requires only 8 bytes of overhead.
It breaks the data packet into datagrams.
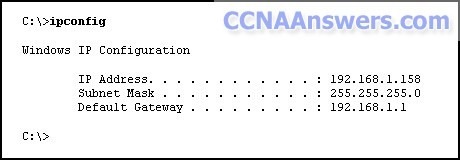
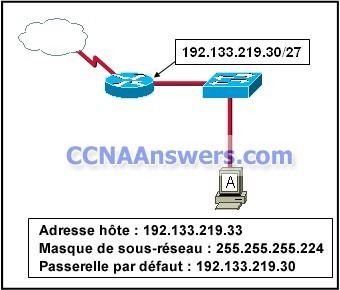
36.
Refer to the exhibit. A computer with the displayed IP settings is unable to access a server on the 192.168.2.0 network using the server IP address but can access hosts on the 192.168.1.0 network. What should the network administrator do to troubleshoot this problem?
Issue the ping 192.168.1.1 command on the host to determine if the host can communicate with the default gateway.
Issue the ipconfig /all command to determine if a DNS server IP address was configured.
Verify that the host has a link light.
Check the cabling of the host.
37. Which address does a switch use for implementing port security?
the source IP address
the source MAC address
the destination IP address
the destination MAC address
38. Which two parameters are stored in the routing table? (Choose two.)
the best route to reach remote networks
the interfaces used to forward packets
the ARP requests from connected routers
the number of times a route has been used by the router
the packets that are placed in the buffer before being forwarded
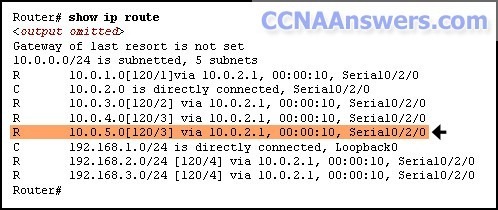
39.
Refer to the exhibit. What does the highlighted value 120 represent?
the number of hops between the router and network 10.0.5.0
the administrative distance of the routing protocol
the UDP port number that is used for forwarding traffic
the bandwidth that is allocated to the serial interface
40. What is an example of a dedicated point-to-point WAN link?
ISDN
Frame Relay
dialup
T1/E1
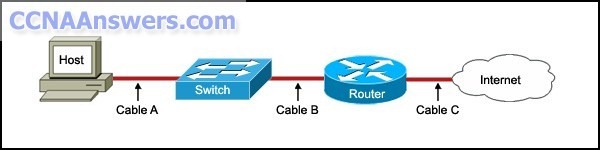
41.
Refer to the exhibit. Which combination of cable types should be used to complete the connection?
Cable A - straight-through; Cable B - straight-through; Cable C - serial
Cable A - straight-through; Cable B - straight-through; Cable C - rollover
Cable A - rollover; Cable B - straight-through; Cable C - crossover
Cable A - straight-through; Cable B - crossover; Cable C – serial
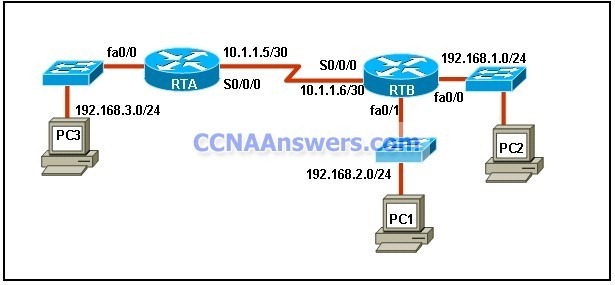
42.
Refer to the exhibit. The network administrator uses the command below to configure a default route on RTB:
RTB(config)# ip route 0.0.0.0 0.0.0.0 fa0/0
A ping issued from PC3 is successful to RTB. However, echo request packets arrive at PC1 but the echo replies do not make it back to PC3. What will fix this problem?
RTA must be configured to forward packets to the 192.168.2.0 network.
The ip route command needs to be edited so that the next hop address is 10.1.1.5.
The ip route command needs to be edited so that the 192.168.2.1 address is the next hop address.
The ip route command should be removed from the RTB router configuration.
Another default route should be configured on RTA with a next hop address of 10.1.1.6.
43. How do port filtering and access lists help provide network security?
They prevent specified types of traffic from reaching specified network destinations.
They alert network administrators to various type of denial of service attacks as they occur.
They prevent viruses, worms, and Trojans from infecting host computers and servers.
They enable encryption and authentication of confidential data communications.
44. A tracert command is run on a host to determine if another host can be reached across a network. Which two events will occur if connectivity with the other host is unsuccessful? (Choose two.)
The command will display all the successful hops a packet makes before it is lost.
The command will calculate the time between successful and unsuccessful packets.
The host on which the command is run will send a UDP request message to the other host.
The command helps to determine where a packet was lost on the path from the source to the destination.
All hops between the two hosts display !!!!! to signify success.
45. A building has experienced a power outage. When the power returns, none of the devices on one floor can access the Internet. The network administrator checks the switch in the IDF that these devices are connected to and notes that the SYST LED on the front of the switch is amber.
What is a possible cause of this problem?
The switch is functioning properly.
The switch has failed POST.
The switch configuration file was not saved to NVRAM.
The connection between the switch and the server did not autonegotiate speed and duplex properly.
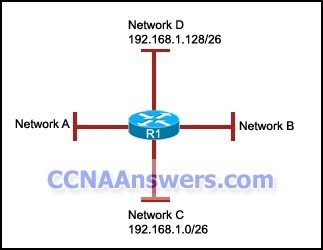
46.
Refer to the exhibit. The network administrator has added networks A and B to router R1. Which two subnetwork numbers should be used to address networks A and B so that these networks use the same subnet mask as networks C and D? (Choose two.)
192.168.1.32/26
192.168.1.64/26
192.168.1.96/26
192.168.1.160/26
192.168.1.192/26
47. If the start-up configuration is not found in NVRAM, where will the router look for it next by default?
flash
ROM
RAM
TFTP server
48. What is the basis for determining the vector component of a route in the distance vector routing algorithm?
the bandwidth of the route
the reliability of the route
the IP address of the next hop
the number of hops
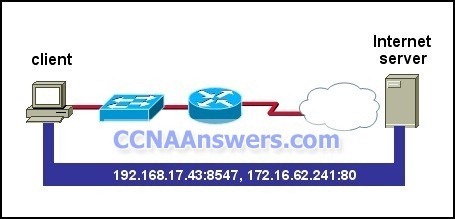
49.
Refer to the exhibit. Which two statements describe the data conversation shown? (Choose two.)
The data conversation was started by the HTTP application process running on the client.
The data conversation is identified by TCP port 80 on the client.
The user started the data conversation by sending an e-mail.
The IP address of the Internet server is 192.168.17.43.
The Internet server will send data to port 8547 on the client.
50. What is the function of the forward lookup DNS zone in the DNS name resolution process?
It resolves fully qualified domain names into IP addresses.
It stores the information about the domain namespace structure.
It forwards zone information updates to the secondary server.
It maintains a database of ARP entries for all servers.
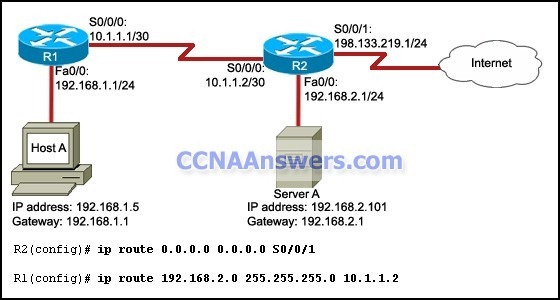
51.
Refer to the exhibit. The interfaces on R1 and R2 have been properly configured with the IP addresses as shown. No dynamic routing protocols have been configured. The network administrator has entered the commands that are shown in the exhibit.
Which two additional commands need to be entered on the routers to enable host A to access the Internet? (Choose two.)
R2(config)# ip route 0.0.0.0 0.0.0.0 S0/0/0
R1(config)# ip route 0.0.0.0 0.0.0.0 S0/0/0
R1(config)# ip route 0.0.0.0 0.0.0.0 198.213.219.1
R2(config)# ip route 192.168.1.0 255.255.255.0 10.1.1.1
R1(config)# ip route 198.133.219.1 255.255.255.0 10.1.1.2
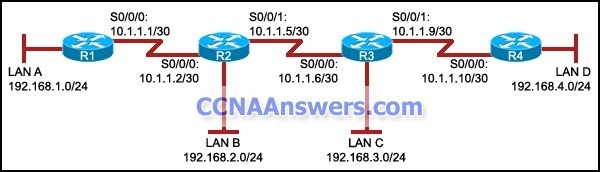
52.
Refer to the exhibit. There is no dynamic routing protocol that is running on this network. The network administrator adds a static route via the use of the ip route 192.168.4.0 255.255.255.0 10.1.1.6 command. On which router should the network administrator issue this command?
R1
R2
R3
R4
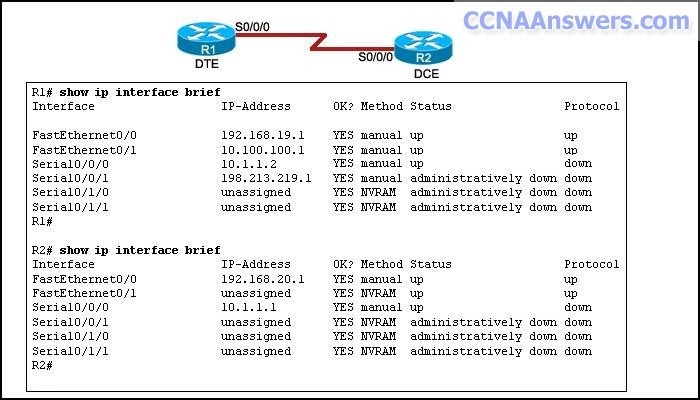
53.
Refer to the exhibit. A network administrator is troubleshooting the serial connection between R1 and R2. There is no communication between R1 and R2. Based on the output of the show ip interface brief command, what is the cause of the problem?
There is a misconfiguration of IP addresses.
There is a mismatch of encapsulation methods.
The no shutdown command has not been issued on R2.
The routing protocols are not compatible.
54. Which two services are required to enable a computer to receive dynamic IP addresses and access the Internet using domain names? (Choose two.)
DNS
WINS
HTTP
DHCP
SMTP
55. The network administrator can ping a remote router but is unable to telnet to it. At what layer of the OSI model does this error occur?
physical
network
data link
application
56. What will a router do with a packet that is destined for a host with the IP address 192.168.1.5/24 if no entry for the 192.168.24.0/24 network exists in the routing table?
It will broadcast the packet out of all of its active interfaces except the interface that received the packet.
It will send the packet back to the source address.
It will drop the packet.
It will broadcast the packet out of all of its active interfaces.


Leave a Reply