CCNA 4 Module 3 V3.1 Answers
1. A technician is testing the functionality of a recently installed router. The technician is unable to ping the serial interface of a remote router. The technician executes the show interface serial 0/0 command on the local router and receives the following output:
Serial0/0 is up, line protocol is down(disabled)
What are possible causes for this command output? (Choose two.)
interface missing the no shutdown command
clockrate command missing
CSU/DSU failed
interface shutdown due to high error rate
cable missing
2. A technician has used Telnet to gain remote access to a router that has no connectivity on its serial interface. Which command should be issued to determine if the serial cable is connected properly?
show controllers
show processes
show run
show status
3. A two router network is running PPP over the serial interfaces that connect them. The enable password on the Denim router is "gateway". The Denim router also has a locally configured authentication password for the Plaid router which is "fortress". Which command must be executed on the Plaid router to allow Denim to authenticate to the Plaid router using CHAP?
Plaid(config)# enable secret gateway
Plaid(config)# enable secret fortress
Plaid(config)# username Plaid password fortress
Plaid(config)# username Denim password fortress
Plaid(config)# hostname Plaid secret password gateway
Plaid(config)# hostname Plaid secret password fortress
4.
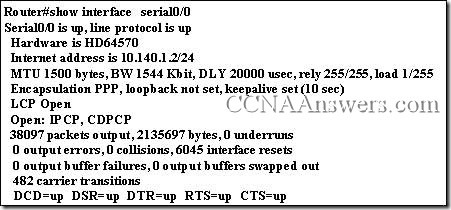
Refer to the output of the show interface Serial0/0 command in the graphic. How many NCPs have been established?
1
2
3
4
5. Which command specifies a link quality over a PPP link?
ppp link 50
ppp link quality 60
ppp percentage 80
ppp quality 90
6. When troubleshooting the Serial 0/0 interface of a router, a technician issues the show controllers command. The following was the output of the command:
Interface is Serial0/0, electrical interface is UNKNOWN.
What can be concluded about the Serial 0/0 interface? (Choose three.)
Serial0/0 is down, line protocol is down
Serial0/0 is down, line protocol is up
Serial0/0 is up, line protocol is down
The interface is neither DCE or DTE.
The interface hardware may be faulty.
The cabling may be improperly connected.
7. Which of the following is a reason for using such protocols as PAP and CHAP?
to establish a PPP session
to provide error checking on a WAN link
to restrict access to networks connected by serial and ISDN links
to provide a backup hostname and privilege mode password on the router
8. Several tasks must occur before a link between two routers can pass data using PPP. Which of the following are required to establish and maintain a PPP session between two routers?
configure each host with a PPP address
configure authentication between the two routers
send LCP and NCP frames to negotiate configuration parameters
send hostname and password information between the two routers
9. Which of the following describes the High-Level Data Link Control protocol? (Choose three.)
HDLC provides flow and error control.
Standard HDLC supports multiple protocols on a single link.
HDLC uses sequencing and acknowledgements.
HDLC is defined as the default encapsulation on Cisco LAN interfaces.
Cisco implemented a proprietary version of HDLC.
10. Which authentication protocol can be spoofed to allow playback attacks?
MD5
CHAP
PAP
NCP
11. ISDN BRI service uses two B channels to send data, voice, and video. If the first channel becomes saturated, the second channel can be configured to forward packets. Which command will allow ISDN to load balance across both links?
Router(config-if)# ppp quality 2
Router(config-if)# ip variance
Router(config-if)# ip maximum-paths 2
Router(config-if)# ppp multilink
12. PPP uses several protocols for communication. Which of the following are options that the LCP protocol in the PPP architecture can provide? (Choose two.)
testing the quality of the link
routing packets between devices
assigning individual station addresses
configuring network layer protocols
negotiating authentication options
13. How did Cisco alter the HDLC encapsulation to allow a single link to carry multiple protocols?
split the transmissions into multiple channels each carrying a single protocol
identified the protocol in the FCS field
compressed the datagrams differently for each protocol
added a type field to identify the protocol
14. Which of the following is an advantage of using time-division multiplexing (TDM) for transmitting data? (Choose two.)
It allows a single source to transmit over multiple data channels.
Multiple sources can transmit over a single channel.
Original data streams must be reconstructed at the destination.
TDM relies on Layer 3 protocols to operate.
15.
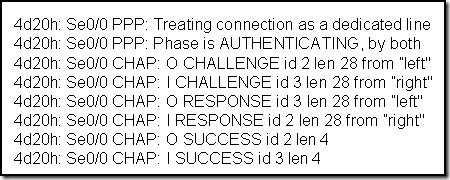
What can be concluded from the output shown in the graphic? (Choose three.)
A two-way handshake is occuring.
The LCPs were already negotiated.
The router can begin NCP negotiations.
The debug ppp negotiation command was executed.
The debug ppp authentication command was executed.
16.
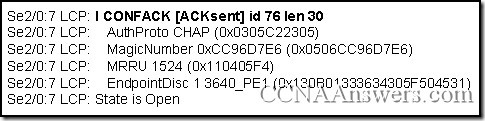
Which command was used to display the partial output shown in the graphic?
show ppp traffic
show lcp traffic
debug ppp negotiation
debug ppp authentication
17. How is the MD5 function valuable in authentication? (Choose two.)
uses a one-way hash function
authentication occurs more rapidly
challenges are unique
the remote router assumes control of frequency of challenge
the remote router assumes control of timing of challenge
18. What are three features of the CHAP protocol? (Choose three.)
exchanges a random challenge number during the session to verify identity
sends authentication password to verify identity
prevents transmission of login information in plain text
disconnects the PPP session if authentication fails
initiates a two-way handshake
19. Which of the following describe functions of the Point-to-Point protocol with regards to the OSI model? (Choose three.)
PPP uses Layer 3 of the OSI model to establish and maintain a session between devices.
PPP operates at all layers of the OSI model.
PPP uses the data link layer to configure such options as error detection and compression.
PPP provides a mechanism to multiplex several network layer protocols.
PPP uses Network Control Protocols (NCP) to test and maintain connectivity between devices.
PPP can be configured on both synchronous and asynchronous serial interfaces.
20. Which advantage does the multilink option provide when using PPP?
Data transmission has load balancing possibilities.
Interfaces can be configured using both HDLC and PPP.
More than one authentication method can be used.
More than one compression protocol can be configured.



Leave a Reply