CCNA 1 Chapter 1 V5.0 Answers
1. What two criteria are used to help select network media? (Choose two.)
the types of data that need to be prioritized
the cost of the end devices utilized in the network
the distance the media can successfully carry a signal
the number of intermediary devices installed in the network
the environment where the media is to be installed
2. Which device performs the function of determining the path that messages should take through internetworks?
a router
a firewall
a web server
a DSL modem
3. What is a characteristic of circuit-switched networks?
If all circuits are busy, a new call cannot be placed.
If a circuit fails, the call will be forwarded on a new path.
Circuit-switched networks can dynamically learn and use redundant circuits.
A single message can be broken into multiple message blocks that are transmitted through multiple circuits simultaneously.
4. Which expression accurately defines the term congestion?
a method of limiting the impact of a hardware or software failure on the network
a measure of the data carrying capacity of the network
a state where the demand on the network resources exceeds the available capacity
a set of techniques to manage the utilization of network resources
5. Which tool provides real-time video and audio communication over the Internet so that businesses can conduct corporate meetings with participants from several remote locations?
wiki
weblog
TelePresence
instant messaging
6. Which description correctly defines a converged network?
a single network channel capable of delivering multiple communication forms
a network that allows users to interact directly with each other over multiple channels
a dedicated network with separate channels for video and voice services
a network that is limited to exchanging character-based information
7. Requiring strong, complex passwords is a practice that supports which network security goal?
maintaining communication integrity
ensuring reliability of access
ensuring data confidentiality
ensuring redundancy
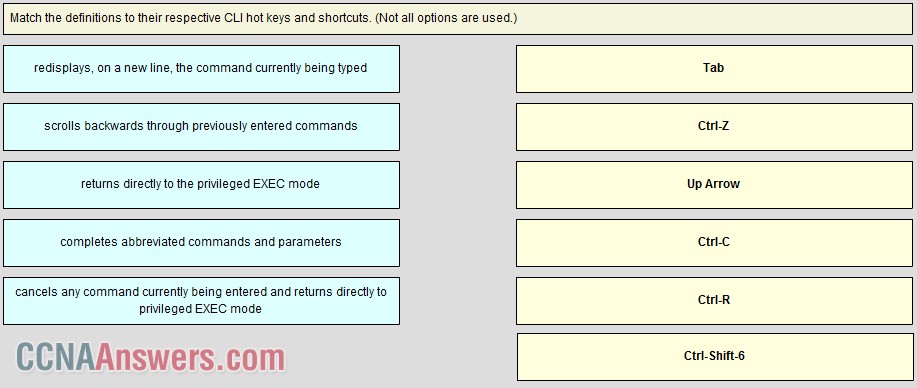
8. Drag and drop
Match each definition to the corresponding security goal
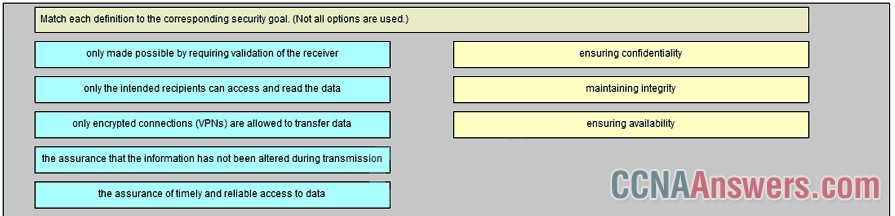
maintaining integrity -> the assurance that the information has not been altered during transmission
ensuring confidentiality -> only the intended recipients can access and read the data
ensuring availability -> the assurance of timely and reliable access to data
9. Drag and drop
Match the form of network communication with its description
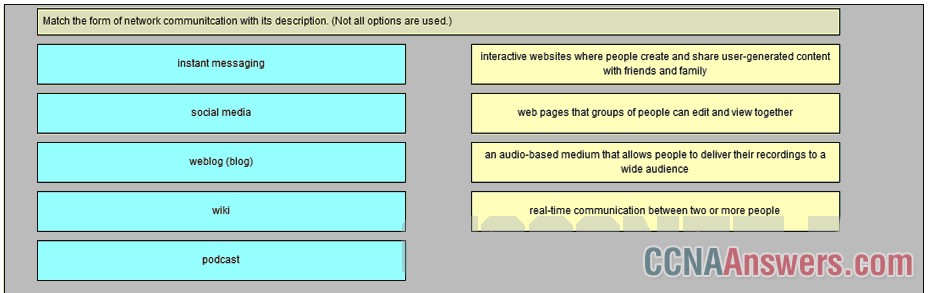
web pages that groups of people can edit and view together -> wiki
interactive websites where people created and share user-generated content with friends and family -> social media
real-time communication of between two or more people -> instant messaging
an audio-based medium that allows people to deliver their recordings to a wide audience -> podcast
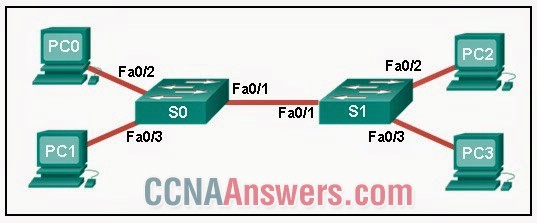
10.
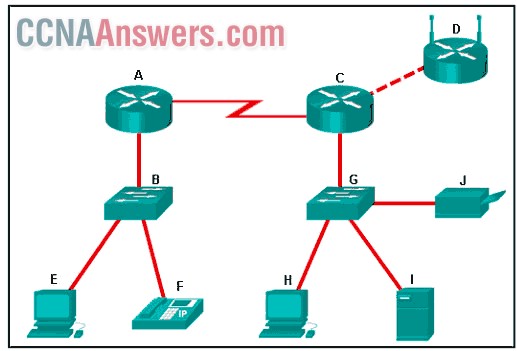
Refer to the exhibit. Which set of devices contains only intermediary devices?
A, B, D, G
A, B, E, F
C, D, G, I
G, H, I, J
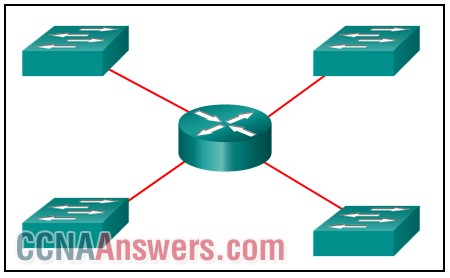
11. What are two functions of intermediary devices on a network? (Choose two.)
They are the primary source and providers of information and services to end devices.
They run applications that support collaboration for business.
They form the interface between the human network and the underlying communication network.
They direct data along alternate pathways when there is a link failure.
They filter the flow of data, based on security settings.
12. Which statement describes a network that supports QoS?
The fewest possible devices are affected by a failure.
The network should be able to expand to keep up with user demand.
The network provides predictable levels of service to different types of traffic.
Data sent over the network is not altered in transmission.
13. Which statement describes a characteristic of cloud computing?
A business can connect directly to the Internet without the use of an ISP.
Applications can be accessed over the Internet through a subscription.
Devices can connect to the Internet through existing electrical wiring.
Investment in new infrastructure is required in order to access the cloud.
14. What type of network must a home user access in order to do online shopping?
an intranet
the Internet
an extranet
a local area network
15. Which two statements about the relationship between LANs and WANs are true? (Choose two.)
Both LANs and WANs connect end devices.
WANs connect LANs at slower speed bandwidth than LANs connect their internal end devices.
LANs connect multiple WANs together.
WANs must be publicly-owned, but LANs can be owned by either public or private entities.
WANs are typically operated through multiple ISPs, but LANs are typically operated by single organizations or individuals.
16. Which two Internet solutions provide an always-on, high-bandwidth connection to computers on a LAN? (Choose two.)
cellular
DSL
satellite
cable
dial-up telephone
17. Drag and drop
Match each characteristic to its corresponding internet conectivity type
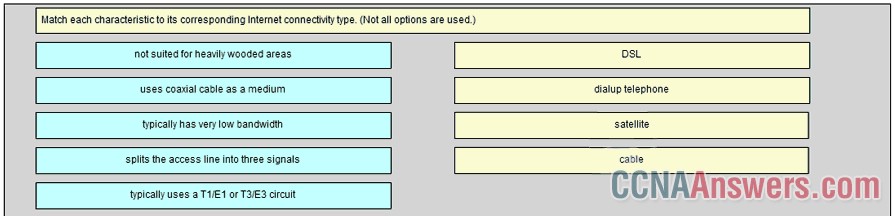
satellite -> not suited for heavily wooded areas
dialup telephone -> typically has very low bandwidth
DSL -> splits the access line into three signals
cable -> uses coaxial cable as a medium
18. Which area of the network would a college IT staff most likely have to redesign as a direct result of many students bringing their own tablets and smartphones to school to access school resources?
extranet
intranet
wired LAN
wireless LAN
wireless WAN
19. Which three network tools provide the minimum required security protection for home users? (Choose three.)
an intrusion prevention system
antivirus software
antispyware software
access control lists
a firewall
powerline networking
20. Which two Internet connection options do not require that physical cables be run to the building? (Choose two.)
DSL
cellular
satellite
dialup
dedicated leased line


Leave a Reply