CCNA 2 Final Exam V4.0 Answers
1.
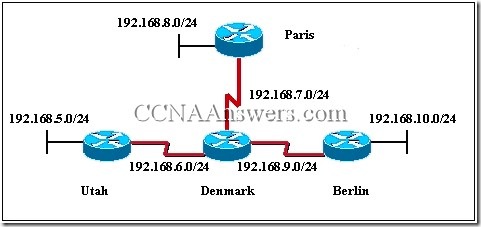
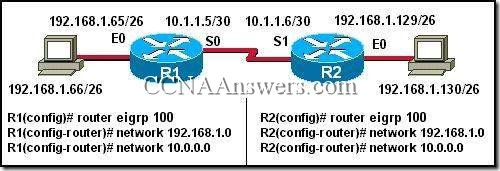
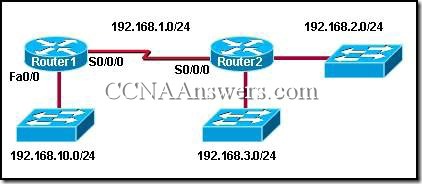
Refer to the exhibit. Given the topology shown in the exhibit, what three commands are needed to configure EIGRP on the Paris router? (Choose three.)Paris(config)# router eigrp 100
Paris(config)# router eigrp
Paris(config-router)# network 192.168.6.0
Paris(config-router)# network 192.168.7.0
Paris(config-router)# network 192.168.8.0
Paris(config-router)# network 192.168.9.0
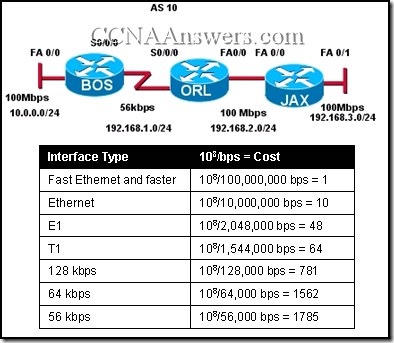
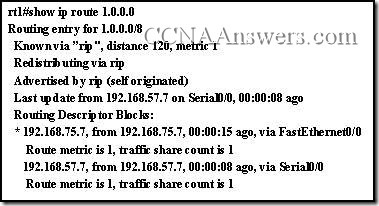
2. In a lab test environment, a router has learned about network 172.16.1.0 through four different dynamic routing processes. Which route will be used to reach this network?
D 172.16.1.0/24 [90/2195456] via 192.168.200.1, 00:00:09, Serial0/0/0
O 172.16.1.0/24 [110/1012] via 192.168.200.1, 00:00:22, Serial0/0/0
R 172.16.1.0/24 [120/1] via 192.168.200.1, 00:00:17, Serial0/0/0
I 172.16.1.0/24 [100/1192] via 192.168.200.1, 00:00:09, Serial0/0/0